Security - Do you have a strict password security policy?
Last updated by Brady Stroud [SSW] about 1 year ago.See historyThe standard is to enforce policies based on reputable regulatory organizations (e.g. NIST, ACSC) latest recommendations.
When passwords have to be changed they should meet the following complexity requirements:
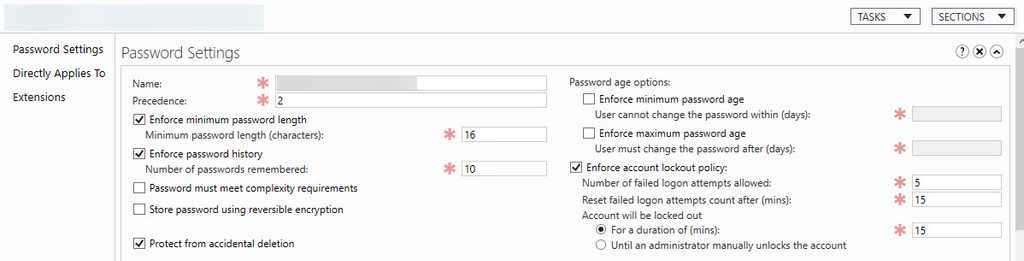
- Ignore password complexity (numbers, special characters, spaces) but require longer passwords - E.g. Require 16 characters length minimum, without special characters or numbers
- Longer passphrases are better than passwords - They are even more difficult to crack than complex passwords
- Longer password history remembered - E.g. Cannot use the last 10 passwords you already used
- Blocking of common password and words – E.g. Via Azure AD Password Protection
- Use of MFA (Multi Factor Authentication) everywhere possible
- Use a password manager
- Use different passwords for every service
- Enforce a lockout policy - E.g. If a user gets their password wrong 5 times, their account will be locked out for 15 minutes
Important: Requiring users to change their passwords (e.g. every 180 days) does not improve security. If you already have a strong password (as above) and a second factor of authentication (e.g. MFA), changing it does very little to make you more secure. Generally, you should change your password only when you believe it has been compromised.